I was asked recently whether a certain app or service required the .NET framework and while I generally knew the answer was no, I had no proof. I kept thinking, how can I determine what apps on this server were actually .NET? The following is a quick way to find those apps.
Microsoft Sysinternals Suite is an excellent set of utilities used to get under the hood of Windows and various Microsoft services. You can download the individual utilities but I just download the entire Suite. This post will use Process Explorer from the Suite but will barely scratch the surface of this powerful utility.
http://technet.microsoft.com/en-us/sysinternals/bb842062
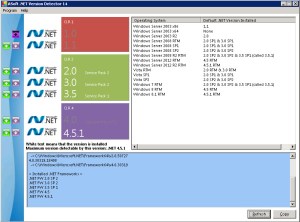
To find out what .NET assembly versions you have installed, run Asoft’s .NET Version Detector. There is more to .NET detection than just looking in Add/Remove Programs, Program Files or the Registry.
http://www.asoft.be/prod_netver.html
1) Download and unzip Asoft’s .NET Version Detector. Double-click the dotnet.exe file, click OK on the license page and it will render your versions on the left and in the lower section. On the right they conveniently provide you with the default .NET version for each Windows OS. This is a great time saver. Thanks Asoft devs!
2) Download the Sysinternals Suite at the URL above or just download Process Explorer itself. Unzip and copy the procexp.chm and procexp.exe files to C:\Windows\System32 or if you don’t want to place them in System32 just park them in a location of your choice. Process Explorer is standalone so no installation is required.
3) In order to access the .NET tabs, it must be run as Administrator. I prefer to execute it from the CLI. Start > enter cmd.exe in the search field and cmd.exe will appear at the top. Right-click it and select Run As Administrator. If you didn’t place it in the System32 folder, change directories to the location of procexp.exe. To run it just type procexp.exe and press enter. You can also just right-click the procexp.exe file and select Run As Administrator. Click Yes on the User Account Control pop-up window.
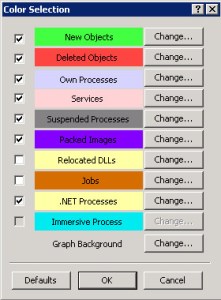
4) Select Options > Configure Colors.
5) Select the check box next to .Net Processes in the yellow box and click OK. This will highlight .NET processes in yellow.
6) Scroll up and down in the process column and look for yellow highlighted entries. Note that there may not be any. If you suspect that an application might be a .NET application simply start it and check the process column again for that app. In this case, the first instance I find is Microsoft AD web services.
7) Right-click the service that is highlighted in yellow and select Properties. Select the .NET Assemblies and .NET Performance tabs to dig deeper into the service.
8) A less useful but honorable mention goes to wmic. It provides the installed version but little else. I need to play around with it a bit more and see what I can find. Running the command below will provide the installed version and takes about 30 seconds to run.
C:\Windows\system32> wmic product where “Name like ‘Microsoft .Net%'” get Name, Version
Name Version
Microsoft .NET Framework 4.5.1 4.5.50938