This is a companion post to sniffing packets in ESXi I posted here.
Say you need to isolate traffic to troubleshoot iSCSI CHAP session negotiation failures between ESXi and NetApp storage.
Using Wireshark:
1) Dump the traffic to a pcap file and open it with Wireshark. Before you start the capture, change directories so you can easily recover the pcap file from the datastore in vCenter.
> cd /vmfs/volumes/datastore1
> tcpdump-uw -i vmk1 -s 1514 -w esxihost01.pcap
> CTRL+C
a) When done, in vCenter select the ESXi host you were sniffing packets on, then click the Configuration tab > Storage.
b) Right-click datastore1 (or the datastore were your pcap file is) and select Browse datastore.
c) Click download a file > select the location and click OK.
d) Double-click the file and it will open in Wireshark.
e) In Wireshark, in the upper left, enter iscsi.login.T in the Filter: field and click Apply. This only shows the iSCSI login packets. You can clearly see on the right in the Info column, packet 856 is an Authentication Failure packet.
Using Splunk:
Another way to see the authentication failure is with Splunk. Assuming your NetApp storage (or any vendor) is configured to send syslog to Splunk, you can easily find the event. Splunk is an excellent Syslog server. You can download and use it for free up to 500 Megs a day indexed. I won’t go into the Splunk configuration in this post. I’ll post that soon.
Download it from here: http://www.splunk.com/download?r=header
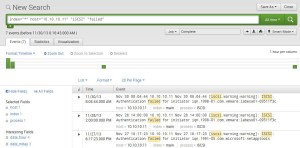
1) Login to the Splunk UI, click Search to launch the Search app, enter the string below and the results will be displayed.
> index=”*” host=”10.10.10.11″ “iSCSI” “failed”
– Note: replace the IP address with your storage controller hostname or IP.