This post demonstrates how to enable two-way or mutual CHAP on iSCSI luns between Debian Linux 7.1 and NetApp storage. The aggregate, lun and disk sizes are small in this HOWTO to keep it simple.
1) Install open-iscsi on your server.
> apt-get install open-iscsi
> reboot (don’t argue with me, just do it!)
2) Display your server’s new iscsi initiator or iqn nodename.
> cat /etc/iscsi/initiatorname.iscsi
InitiatorName=iqn.1993-08.org.debian:01:e6d4ee61d916
3) On the NetApp filer, create the volume that will hold the iscsi luns. This command assumes you have aggregrate aggr1 already created. If not use an aggregate that has enough room for your volume.
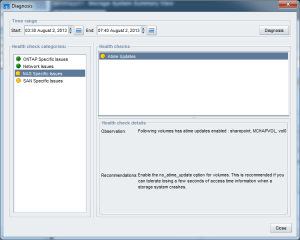
netapp> vol create MCHAPVOL aggr1 10g
4) Create the lun in the volume.
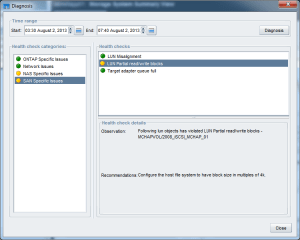
netapp> lun create -s 5g -t linux /vol/MCHAPVOL/DEB71_iSCSI_MCHAP_01
5) Create an igroup and add the Linux iscsi nodename or iqn from step 2 above to it.
netapp> igroup create -i -t linux ISCSI_MCHAP_DEB71
netapp> igroup add ISCSI_MCHAP_DEB71 iqn.1993-08.org.debian:01:e6d4ee61d916
netapp> igroup show
ISCSI_MCHAP_DEB71 (iSCSI) (ostype: linux):
iqn.1993-08.org.debian:01:e6d4ee61d916 (not logged in)
6) Map the lun to the iscsi-group and give it lun ID 01.
netapp> lun map /vol/MCHAPVOL/DEB71_iSCSI_MCHAP_01 ISCSI_MCHAP_DEB71 01
7) Obtain the NetApp target nodename.
netapp> iscsi nodename
iqn.1992-08.com.netapp:sn.84167939
8) Set the CHAP secret on the NetApp controller.
netapp> iscsi security add -i iqn.1993-08.org.debian:01:e6d4ee61d916 -s chap -p MCHAPDEB71 -n iqn.1993-08.org.debian:01:e6d4ee61d916 -o NETAPPMCHAP -m iqn.1992-08.com.netapp:sn.84167939
netapp> iscsi security show
init: iqn.1993-08.org.debian:01:e6d4ee61d916 auth: CHAP Inbound password: **** Inbound username: iqn.1993-08.org.debian:01:e6d4ee61d916 Outbound password: **** Outbound username: iqn.1992-08.com.netapp:sn.84167939
9) On the server, edit your /etc/iscsi/iscsi.conf file and set the parameters below.
> vi /etc/iscsi/iscsid.conf:
node.startup = automatic
node.session.auth.authmethod = CHAP
node.session.auth.username = iqn.1993-08.org.debian:01:e6d4ee61d916
node.session.auth.password = MCHAPDEB71
node.session.auth.username_in = iqn.1992-08.com.netapp:sn.84167939
node.session.auth.password_in = NETAPPMCHAP
discovery.sendtargets.auth.authmethod = CHAP
discovery.sendtargets.auth.username = iqn.1993-08.org.debian:01:e6d4ee61d916
discovery.sendtargets.auth.password = MCHAPDEB71
discovery.sendtargets.auth.username_in = iqn.1992-08.com.netapp:sn.84167939
discovery.sendtargets.auth.password_in = NETAPPMCHAP
> wq!
10) On the server, discover your iSCSI target (your storage system).
> iscsiadm -m discovery -t st -p 10.10.10.11
10.10.10.11:3260,1000 iqn.1992-08.com.netapp:sn.84167939
> iscsiadm -m node (this should display the same as above)
10.10.10.11:3260,1000 iqn.1992-08.com.netapp:sn.84167939
11) On the server, manually login to the iSCSI target (your storage array).
> iscsiadm -m node –targetname “iqn.1992-08.com.netapp:sn.84167939” –login
Logging in to [iface: default, target: iqn.1992-08.com.netapp:sn.84167939, portal: 10.10.10.11,3260] (multiple)
Login to [iface: default, target: iqn.1992-08.com.netapp:sn.84167939, portal: 10.10.10.11,3260] successful.
On the NetApp storage console you should see the iSCSI sessions:
[iscsi.notice:notice]: ISCSI: New session from initiator iqn.1993-08.org.debian:01:e6d4ee61d916 at IP addr 10.10.10.203
[iscsi.notice:notice]: ISCSI: New session from initiator iqn.1993-08.org.debian:01:e6d4ee61d916 at IP addr 10.10.10.203
Verify the iSCSI session on the filer:
netapp> iscsi session show
Session 49
Initiator Information
Initiator Name: iqn.1993-08.org.debian:01:e6d4ee61d916
ISID: 00:02:3d:01:00:00
Initiator Alias: deb71
12) Stop and start the iscsi service on the server.
> service open-iscsi stop
Pause for 10 seconds and then run the next command.
> service open-iscsi start
[ ok ] Starting iSCSI initiator service: iscsid.
[….] Setting up iSCSI targets:
Logging in to [iface: default, target: iqn.1992-08.com.netapp:sn.84167939, portal: 10.10.10.11,3260] (multiple)
Login to [iface: default, target: iqn.1992-08.com.netapp:sn.84167939, portal: 10.10.10.11,3260] successful.
. ok
[ ok ] Mounting network filesystems:.
13) From the server , check your session.
> iscsiadm -m session -P 1
14) From the server, check the NetApp iSCSI details.
> iscsiadm –mode node –targetname “iqn.1992-08.com.netapp:sn.84167939” –portal 10.10.10.11:3260
15) From the server, find and format the new lun (new disk).
> cat /var/log/messages | grep “unknown partition table”
deb71 kernel: [ 1856.751777] sdb: unknown partition table
> fdisk /dev/sdb
Device contains neither a valid DOS partition table, nor Sun, SGI or OSF disklabel
Building a new DOS disklabel with disk identifier 0x07f6c360.
Changes will remain in memory only, until you decide to write them.
After that, of course, the previous content won’t be recoverable.
Warning: invalid flag 0x0000 of partition table 4 will be corrected by w(rite)
Command (m for help): w
The partition table has been altered!
Calling ioctl() to re-read partition table.
Syncing disks.
Command (m for help): n
Partition type:
p primary (0 primary, 0 extended, 4 free)
e extended
Select (default p): p
Partition number (1-4, default 1): 1
First sector (2048-10485759, default 2048): press enter
Using default value 2048
Last sector, +sectors or +size{K,M,G} (2048-10485759, default 10485759): press enter
Using default value 10485759
Command (m for help): p
Disk /dev/sdb: 5368 MB, 5368709120 bytes
166 heads, 62 sectors/track, 1018 cylinders, total 10485760 sectors
Units = sectors of 1 * 512 = 512 bytes
Sector size (logical/physical): 512 bytes / 512 bytes
I/O size (minimum/optimal): 512 bytes / 512 bytes
Disk identifier: 0x07f6c360
Device Boot Start End Blocks Id System
/dev/sdb1 2048 10485759 5241856 83 Linux
Command (m for help): w
The partition table has been altered!
Calling ioctl() to re-read partition table.
Syncing disks.
Command (m for help): q
16) On the server, create the Linux file system on the new partition.
> mkfs -t ext4 /dev/sdb1
mke2fs 1.42.5 (29-Jul-2012)
Filesystem label=
OS type: Linux
Block size=4096 (log=2)
Fragment size=4096 (log=2)
Stride=0 blocks, Stripe width=0 blocks
327680 inodes, 1310464 blocks
65523 blocks (5.00%) reserved for the super user
First data block=0
Maximum filesystem blocks=1342177280
40 block groups
32768 blocks per group, 32768 fragments per group
8192 inodes per group
Superblock backups stored on blocks:
32768, 98304, 163840, 229376, 294912, 819200, 884736
Allocating group tables: done
Writing inode tables: done
Creating journal (32768 blocks): done
Writing superblocks and filesystem accounting information: done
17) Verify the partition.
> blkid /dev/sdb1
/dev/sdb1: UUID=”afba2daf-1de8-4ab1-b93e-e7c99c82c054″ TYPE=”ext4″
18) Create the mount point and manually mount the directory.
> mkdir /newiscsilun
> mount /dev/sdb1 /newiscsilun
> df -h | grep newiscsilun
Filesystem Size Used Avail Use% Mounted on
/dev/sdb1 5.0G 10M 4.7G 1% /newiscsilun
19) Add the new mount point to /etc/fstab.
> vi /etc/fstab
/dev/sdb1 /newiscsilun ext4 _netdev 0 0
> wq!
Note: the _netdev option is important so that it doesn’t try mounting the target before the network is available.
20) Test that it survives a reboot by rebooting the server. With the _netdev set, iscsi starts and your CHAP logins should take place before it attempts to mount. After the reboot, login and verify its mounted.
> df -h | grep newiscsilun
Filesystem Size Used Avail Use% Mounted on
/dev/sdb1 5.0G 10M 4.7G 1% /newiscsilun
21) On the server you can check session stats.
> iscsiadm -m session -s
Stats for session [sid: 1, target: iqn.1992-08.com.netapp:sn.84167939, portal: 10.10.10.11,3260]
iSCSI SNMP:
txdata_octets: 69421020
rxdata_octets: 765756
noptx_pdus: 0
scsicmd_pdus: 365
tmfcmd_pdus: 0
login_pdus: 0
text_pdus: 0
dataout_pdus: 924
logout_pdus: 0
snack_pdus: 0
noprx_pdus: 0
scsirsp_pdus: 365
tmfrsp_pdus: 0
textrsp_pdus: 0
datain_pdus: 193
logoutrsp_pdus: 0
r2t_pdus: 924
async_pdus: 0
rjt_pdus: 0
digest_err: 0
timeout_err: 0
iSCSI Extended:
tx_sendpage_failures: 0
rx_discontiguous_hdr: 0
eh_abort_cnt: 0
22) As root, change permissions on /etc/iscsi/iscsid.conf. I’m not sure why they haven’t fixed this clear text CHAP password in a file issue so just make sure only root can read/write the file.
> chmod 600 /etc/iscsi/iscsid.conf
23) On the NetApp storage you can verify the Lun and the server’s session.
> lun show -v /vol/MCHAPVOL/DEB71_iSCSI_MCHAP_01
/vol/MCHAPVOL/DEB71_iSCSI_MCHAP_01 5g (5368709120) (r/w, online, mapped)
Serial#: hoagPJtrPZCi
Share: none
Space Reservation: enabled
Multiprotocol Type: linux
Maps: ISCSI_MCHAP_DEB71=1
> iscsi session show -v
Session 55
Initiator Information
Initiator Name: iqn.1993-08.org.debian:01:e6d4ee61d916
ISID: 00:02:3d:01:00:00
Initiator Alias: deb71
Session Parameters
SessionType=Normal
TargetPortalGroupTag=1000
MaxConnections=1
ErrorRecoveryLevel=0
AuthMethod=CHAP
HeaderDigest=None
DataDigest=None
ImmediateData=Yes
InitialR2T=No
FirstBurstLength=65536
MaxBurstLength=65536
Initiator MaxRecvDataSegmentLength=65536
Target MaxRecvDataSegmentLength=65536
DefaultTime2Wait=2
DefaultTime2Retain=0
MaxOutstandingR2T=1
DataPDUInOrder=Yes
DataSequenceInOrder=Yes
Command Window Size: 32
Connection Information
Connection 0
Remote Endpoint: 10.10.10.203:57127
Local Endpoint: 10.10.10.11:3260
Local Interface: e0a
TCP recv window size: 131400